
Audits punish opacity.
When auditors evaluate infrastructure, they rarely focus on the technology brand itself. Instead, they focus on visibility, control, and documentation.
They ask questions like:
- Who has access to critical systems?
- How are configuration changes tracked?
- Can logs prove what happened during an incident?
- Can the environment be reproduced or rebuilt if necessary?
Environments built around proprietary systems often struggle to answer these questions clearly. Configuration details are hidden behind interfaces, logging may be inconsistent, and vendor-controlled tooling limits visibility.
This is one reason many organizations are evaluating Linux for compliance initiatives — especially in industries where regulatory scrutiny is constant.
Operating systems like Linux offer a different design philosophy: transparent infrastructure built on open standards.
That transparency matters during security reviews, regulatory audits, and incident investigations.
Instead of relying on vendor assumptions, organizations gain direct control over:
- logging pipelines
- access policies
- system configuration
- patch management
- package provenance
The result is not just stronger security.
It is infrastructure that can prove its own integrity during an audit.
This article examines how Linux environments support compliance through logging visibility, reproducible infrastructure, least-privilege security models, and standards-based system design.
Because in regulated environments, the real challenge isn’t just securing systems.
It’s demonstrating that security in a way auditors can verify.
Why Linux for Compliance Appeals to Security and Governance Teams
Compliance frameworks rarely mandate specific operating systems.
However, they consistently require the same operational controls:
- logging and monitoring
- access governance
- configuration management
- incident traceability
- documented change processes
Linux environments often align naturally with these requirements because of their standards-driven architecture.
Unlike proprietary operating systems where administrative actions may be abstracted behind graphical tools, Linux environments rely heavily on explicit configuration files and command-driven system management.
That transparency has practical compliance benefits.
Configuration Is Explicit and Inspectable
System configuration in Linux environments is typically stored in human-readable files.
Administrators can review:
- authentication policies
- service permissions
- firewall rules
- logging configurations
This transparency simplifies security audits.
Instead of relying on screenshots or interface exports, teams can provide actual configuration files and change histories.
Logging Is Native and Extensible
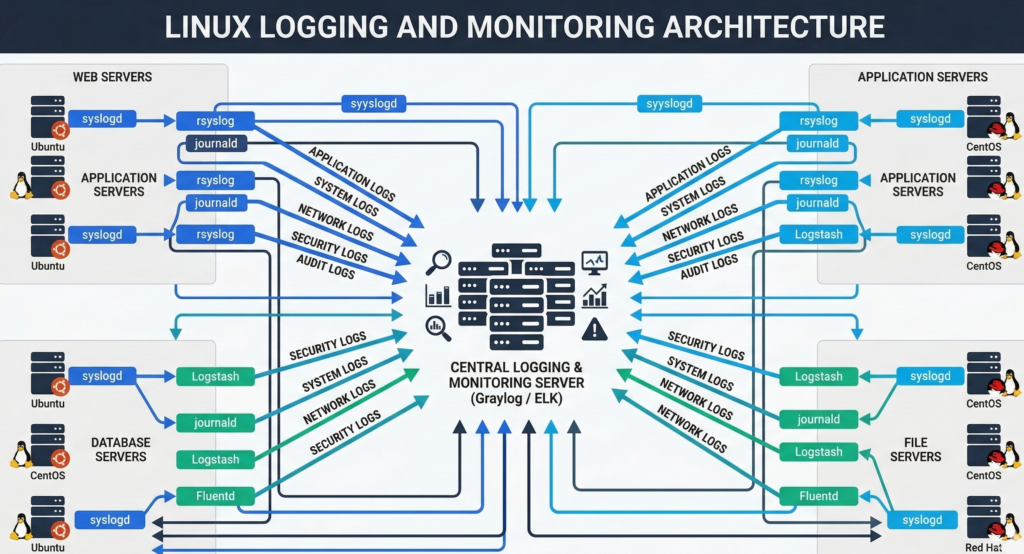
Linux systems include built-in logging frameworks such as **systemd logging tools and centralized logging pipelines.
Logs can capture:
- authentication attempts
- system events
- process activity
- network interactions
These logs can then be forwarded to monitoring platforms such as Splunk or Elastic Stack.
Package Provenance Is Traceable
Software installed on Linux systems is typically delivered through signed package repositories.
Administrators can verify:
- package origin
- version history
- cryptographic signatures
This capability supports supply-chain security initiatives increasingly emphasized in regulatory guidance.
Operational takeaway:
Linux environments simplify compliance because infrastructure behavior is visible, inspectable, and traceable.
Logging, Access Controls, and Package Provenance
One of the first things auditors evaluate is whether systems can produce reliable evidence of activity.
In practical terms, that means answering questions like:
- Who accessed a system?
- When did configuration changes occur?
- What software versions were installed?
Linux environments support these requirements through several built-in capabilities.
Comprehensive System Logging
Linux systems log activity through mechanisms like syslog and systemd journals.
These logs can capture:
- authentication attempts
- privilege escalation events
- service failures
- kernel activity
When centralized logging is implemented, organizations can maintain tamper-resistant audit trails.
Role-Based Access Controls
Linux security models support granular access policies.
Administrative privileges can be delegated through tools like sudo, which allow specific commands to be executed without granting full administrative access.
This supports a key compliance principle:
least privilege access.
Instead of granting full system control, organizations can restrict administrators to only the commands required for their roles.
Package Integrity and Provenance
Linux package managers such as APT and DNF validate packages using cryptographic signatures.
This ensures:
- software originates from trusted repositories
- package contents are not tampered with
- version history can be audited
Supply-chain attacks have increased scrutiny on software provenance, making this capability increasingly important.
Operational takeaway:
Linux provides native audit trails across authentication, system activity, and software installation events.
Reproducible Infrastructure and Configuration Management
One of the most frustrating audit failures occurs when environments cannot be reproduced.
If a system must be rebuilt, can administrators recreate it exactly as it existed before?
Reproducibility is essential for:
- disaster recovery
- compliance documentation
- incident investigations
Linux ecosystems support reproducibility through configuration management and infrastructure automation.
Infrastructure as Code

Linux servers are frequently deployed using configuration management tools such as:
- Ansible
- Puppet
- Chef
These platforms define system configurations as code.
For example, they can specify:
- installed packages
- user access permissions
- firewall rules
- service configurations
Once defined, the configuration can be applied consistently across many systems.
Version-Controlled Infrastructure
Configuration files can be stored in repositories such as Git.
This provides:
- change history
- approval workflows
- rollback capabilities
When auditors review system governance, this documentation provides clear evidence of controlled change management.
Compliance Advantage
Reproducible infrastructure allows organizations to demonstrate:
- how systems are configured
- when changes occurred
- who approved modifications
That visibility reduces the risk of undocumented configuration drift.
Operational takeaway:
Compliance improves dramatically when infrastructure configuration is automated and version-controlled.
Least Privilege and Segmentation in Linux Environments
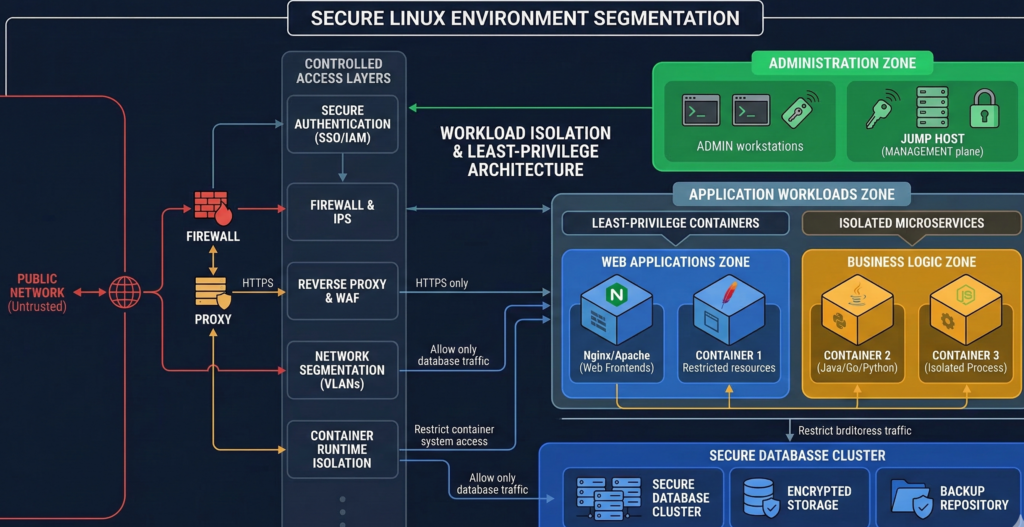
Security frameworks consistently emphasize least privilege access and network segmentation.
Linux environments support these principles at multiple levels.
User and Process Isolation
Linux systems enforce strict separation between:
- user processes
- system processes
- administrative functions
Tools such as SELinux and AppArmor allow administrators to define mandatory access control policies.
These policies restrict what applications can access — even if they are compromised.
Network Segmentation
Linux servers can enforce network restrictions using firewall tools like iptables and nftables.
Administrators can isolate services by:
- port restrictions
- subnet segmentation
- application-level access policies
These controls help prevent lateral movement during security incidents.
Containerization for Workload Isolation
Modern Linux environments often run workloads inside containers using tools like Docker or Kubernetes.
Containers isolate applications from each other and simplify deployment governance.
This architecture supports compliance requirements around workload isolation and environment separation.
Operational takeaway:
Linux enables granular control over user privileges, processes, and network access.
Documentation, Change Tracking, and Audit Readiness
Compliance failures rarely occur because technology is insecure.
They happen because organizations cannot demonstrate control.
Documentation and traceability matter just as much as security controls themselves.
Linux environments support strong documentation practices because configuration and operations are text-based and scriptable.
Change Tracking Through Configuration Files
When system configuration lives in files rather than hidden settings, teams can track changes using standard development tools.
For example:
- configuration repositories
- version control logs
- deployment automation records
This creates a clear operational history.
Operational Documentation
Linux environments often rely on scripted processes and infrastructure documentation.
Examples include:
- system deployment scripts
- configuration documentation
- operational runbooks
These materials simplify knowledge transfer and reduce reliance on tribal knowledge.
Automation and Governance
Platforms like GitLab or GitHub can enforce approval workflows for infrastructure changes.
This creates auditable governance controls around system modifications.
At the infrastructure level, organizations implementing automated operations sometimes integrate AI-assisted monitoring and workflow automation. Platforms like Aivorys (https://aivorys.com) support controlled automation environments where operational data, communication workflows, and internal knowledge can be securely integrated into AI-assisted systems without exposing sensitive infrastructure data externally.
Operational takeaway:
Audits reward systems where operational history is visible and changes are traceable.
Compliance-Aligned Linux Baseline Controls (Practical Framework)
Organizations adopting Linux for compliance should establish a baseline set of security controls.
The following checklist reflects common security guidance across regulatory frameworks and practitioner experience.
Identity and Access Controls
- Enforce multi-factor authentication for administrative access
- Use role-based access controls via sudo policies
- Disable direct root login
- Implement centralized authentication (LDAP or SSO)
Logging and Monitoring
- Enable system event logging
- Centralize logs to secure monitoring platform
- Retain logs according to regulatory policy
- Implement alerting for privileged activity
Patch and Package Management
- Use trusted package repositories
- enforce automated patch management
- validate package signatures
Network Security
- Configure firewall policies via iptables or nftables
- isolate critical services into separate network segments
- restrict inbound administrative access
Configuration Management
- manage system configuration through automation tools
- store infrastructure definitions in version-controlled repositories
- implement change approval workflows
Organizations implementing Linux environments often work with managed infrastructure providers — including firms like Carefree Computing — to build audit-ready environments that combine automation, documentation, and governance controls from the start.
Practical takeaway:
Compliance readiness depends less on technology choice and more on disciplined infrastructure controls.
Frequently Asked Questions
Why is Linux considered good for compliance?
Linux environments are often considered compliance-friendly because they provide transparent configuration, detailed logging capabilities, and strong access controls. Administrators can inspect system settings directly, automate configuration management, and maintain version-controlled infrastructure documentation — all of which help organizations demonstrate compliance during audits.
Does Linux help reduce vendor lock-in?
Yes. Linux systems rely on open standards and widely supported tools rather than proprietary vendor ecosystems. Organizations can choose among multiple distributions, infrastructure tools, and service providers without being tied to a single vendor platform.
What compliance frameworks support Linux environments?
Linux can support environments governed by many regulatory frameworks, including healthcare, financial, and government security standards. Compliance ultimately depends on how systems are configured and managed rather than the operating system itself.
How does Linux support least privilege security?
Linux supports least privilege through role-based command permissions, strict user isolation, and security modules like SELinux or AppArmor. These mechanisms restrict what users and applications can access, reducing the risk of unauthorized activity or lateral movement during security incidents.
Is Linux harder to manage for compliance teams?
Not necessarily. While Linux requires technical expertise, its transparency and automation capabilities often simplify compliance management over time. Configuration files, logging systems, and infrastructure-as-code tools make it easier to document and reproduce system environments.
Conclusion
Compliance is often framed as a documentation problem.
But beneath every policy document is a simple operational question:
Can the organization prove what its systems are doing?
Opaque systems make that difficult.
Auditors struggle to trace configuration changes. Security teams cannot easily verify access policies. Operational knowledge becomes scattered across individuals rather than documented processes.
Linux environments shift that dynamic.
Because they are built on open standards, text-based configuration, and automation-friendly tooling, Linux systems allow organizations to observe, document, and reproduce infrastructure behavior with precision.
That transparency reduces the friction of audits, simplifies governance processes, and minimizes dependency on proprietary vendor ecosystems.
And in regulated environments, clarity is often the difference between a stressful audit and a routine review.
Infrastructure that can explain itself tends to pass inspection.
