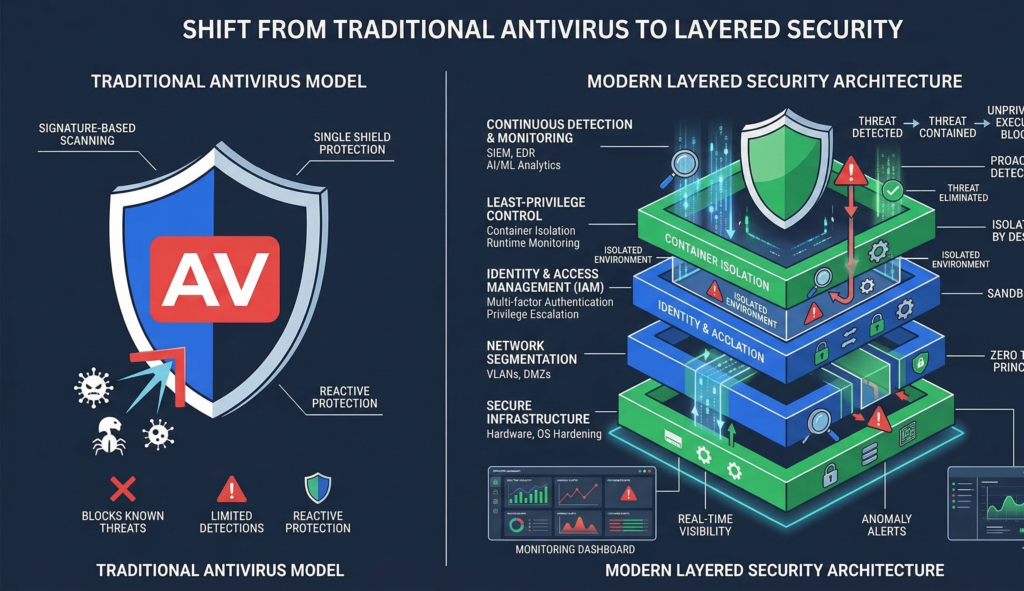
A modern endpoint security strategy must address threats that traditional antivirus can no longer stop.
Today’s attackers use fileless malware, privilege escalation, and sophisticated bypass techniques that easily evade signature-based detection.
Organizations that rely only on antivirus are operating with an outdated security model.
A helpdesk ticket arrives: an employee can’t install a required application.
The fix seems simple. Grant admin privileges so they can complete their work.
Within weeks, the same machine becomes the entry point for a ransomware incident.
The root problem wasn’t the employee, the application, or even the malware.
It was the security model.
For years, organizations relied on traditional antivirus as their primary endpoint defense. But modern attacks move too quickly, mutate too frequently, and increasingly avoid traditional malware signatures entirely.
A resilient endpoint security strategy no longer assumes antivirus will block threats. Instead, it assumes threats will occasionally bypass defenses — and designs systems that contain damage when they do.
This shift has changed how organizations think about endpoint protection. Instead of relying solely on signature-based detection, modern security architectures combine behavioral monitoring, isolation mechanisms, and strict privilege controls.
Operating systems like Linux, virtualization technologies, and endpoint detection platforms now form layered defense systems designed to withstand bypass attempts rather than simply prevent them.
The goal is not perfect prevention.
The goal is controlled failure — where compromised systems cannot compromise the rest of the organization.
Understanding that shift is critical for security leaders building modern endpoint strategies.
Why Signature-Based Antivirus Fails Against Modern Threats
Traditional antivirus relies on signature matching.
When a known piece of malware is identified, its digital fingerprint is added to a detection database. Future scans look for those patterns.
This approach worked when malware changed slowly.
It fails against modern threats.
Polymorphic Malware Evolves Too Quickly
Modern malware often modifies its code automatically each time it spreads.
These polymorphic techniques allow attackers to generate thousands of unique variants of the same malware.
Each variant may evade signature detection until security vendors update their databases.
That delay creates a window for attackers.
Living-Off-the-Land (LOL) Attacks
Many attacks now avoid malware entirely.
Instead, they exploit legitimate tools already present on systems.
Examples include:
- scripting engines
- administrative utilities
- remote management tools
These techniques — commonly called living-off-the-land attacks — are difficult for antivirus systems to detect because they do not involve malicious files.
AI-Generated Attack Variants
Security researchers increasingly observe attack variants generated with AI-assisted tooling.
These systems can:
- generate new payload variants
- alter attack patterns dynamically
- test bypass strategies automatically
The result is a threat landscape where signature databases struggle to keep up.
Security takeaway:
Antivirus remains useful, but it is no longer sufficient as a primary defense mechanism.
The Modern Endpoint Security Strategy: Detection + Containment
Modern security architectures shift the focus from prevention alone to detection and containment.
Instead of assuming malware will always be blocked, systems are designed to:
- detect suspicious behavior
- isolate compromised environments
- prevent lateral movement
This layered approach significantly limits the damage attackers can cause.
Behavior-Based Detection
Behavioral security systems monitor system activity for suspicious patterns.
Instead of looking for known malware signatures, they watch for behaviors such as:
- unexpected privilege escalation
- abnormal network connections
- unusual file system changes
Platforms built around Endpoint Detection and Response frameworks analyze these patterns to detect potential compromise.
Detection Must Lead to Response
Detection alone is insufficient.
Security teams must also define response workflows.
Common responses include:
- isolating the affected endpoint
- terminating suspicious processes
- revoking compromised credentials
These response capabilities transform security monitoring into operational defense.
Security takeaway:
Effective endpoint security combines behavioral detection with automated containment actions.
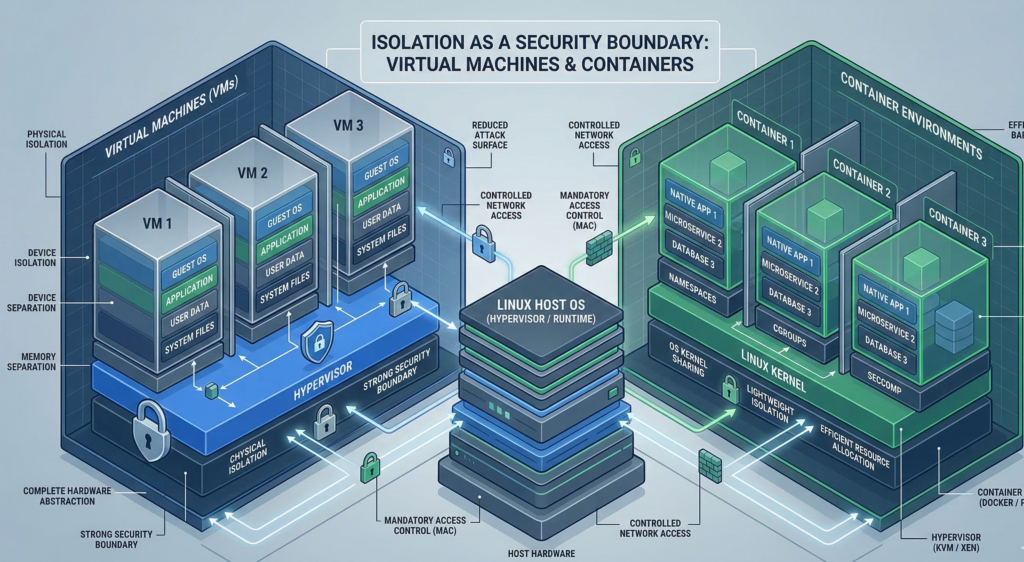
Isolation: Containing Risk With Virtualization and Segmentation
One of the most effective security techniques is also one of the simplest.
Isolation.
Instead of trusting endpoints completely, systems are designed so risky activities occur in controlled environments.
Virtual Machines as Security Boundaries
Virtual machines provide strong isolation between workloads.
If malware infects a virtualized environment, it cannot easily escape to the host system.
Developers, analysts, and researchers often run risky software in isolated VMs to protect primary systems.
Platforms such as KVM and VMware enable this model across enterprise environments.
Containers for Application Isolation
Containers provide a lighter-weight isolation layer.
Technologies like Docker allow applications to run within restricted environments with controlled access to system resources.
This reduces the risk that compromised applications can affect other services.
Linux as a Security Foundation
Many organizations adopt Linux hosts because the platform supports strong isolation capabilities.
Linux security features include:
- namespace isolation
- control groups
- mandatory access controls
Frameworks such as SELinux and AppArmor enforce strict process permissions.
These controls help prevent compromised software from accessing unauthorized resources.
Security takeaway:
Isolation limits damage by ensuring that compromised processes cannot freely access the rest of the system.
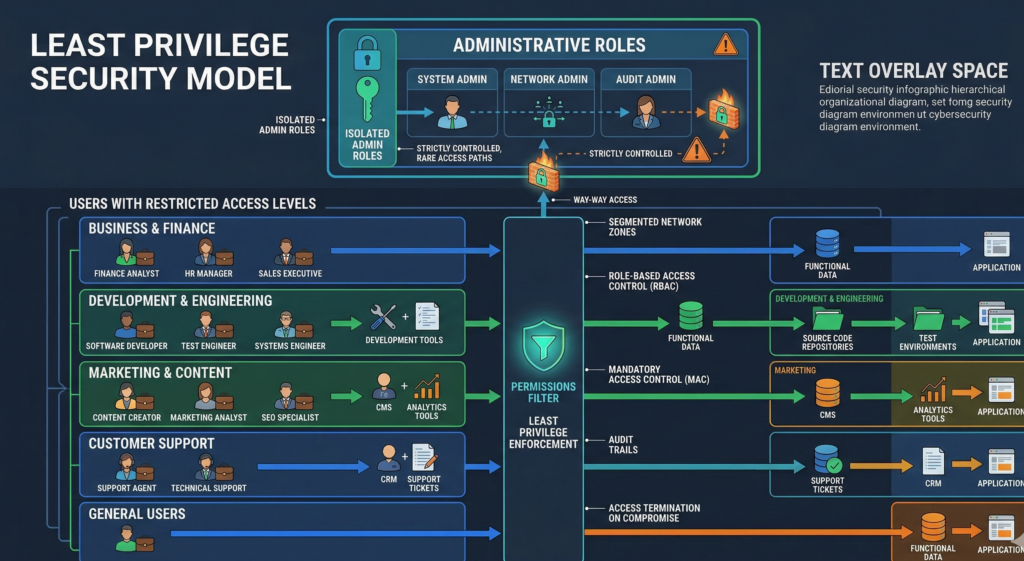
Least Privilege: The Control That Prevents Most Breaches
Many security incidents begin with the same root cause.
Users run with excessive privileges.
Granting administrative rights to simplify workflows often creates the conditions attackers need.
Why Administrator Access Is Dangerous
When users operate as administrators, malicious code inherits those privileges.
This allows attackers to:
- disable security controls
- install persistence mechanisms
- access sensitive data
Removing unnecessary administrative privileges dramatically reduces attack impact.
Implementing the Least Privilege Model
A least privilege architecture ensures users and applications receive only the permissions required for their tasks.
Key practices include:
- role-based access control
- temporary privilege elevation
- privileged session monitoring
Security tools integrated with Active Directory or identity management platforms enforce these policies across organizations.
Operational Reality: Productivity vs Security
The biggest challenge with least privilege is operational friction.
Users still need to perform legitimate tasks.
Modern privilege management systems address this by allowing time-limited privilege elevation rather than permanent admin rights.
Security takeaway:
Least privilege dramatically reduces the blast radius of compromised endpoints.
Logging and Incident Response: Security as an Operational Discipline

Security tools generate alerts.
Operations teams must turn those alerts into action.
Without clear response procedures, detection systems provide little value.
Why Logging Matters
Comprehensive logs enable organizations to:
- detect suspicious patterns
- reconstruct security incidents
- support regulatory compliance
Centralized logging platforms such as Elastic Stack or Splunk collect and analyze security telemetry across systems.
Incident Response Planning
Security teams should define response procedures before incidents occur.
Typical response workflows include:
- identify the compromised endpoint
- isolate it from the network
- investigate attack activity
- restore systems from known-good states
These procedures must be practiced regularly.
Organizations building AI-assisted operational workflows sometimes integrate internal security alerts, documentation, and response playbooks into automation systems. Platforms like Aivorys (https://aivorys.com) support controlled AI-driven workflows connected to internal knowledge bases and operational tools, allowing teams to coordinate response procedures without exposing sensitive security data externally.
Security takeaway:
Security detection must integrate with operational response processes.
Modern Endpoint Strategy Checklist
Organizations updating their endpoint security posture can evaluate their environment using the following framework.
Endpoint Security Readiness Checklist
Privilege Controls
- users do not operate with permanent administrative privileges
- privilege elevation requires approval or justification
- privileged sessions are logged
Isolation Architecture
- risky workloads run in containers or VMs
- development environments are isolated from production systems
- browsers or unknown files run in sandboxed environments
Detection and Monitoring
- endpoint detection tools monitor behavioral activity
- centralized logging aggregates system telemetry
- alerts trigger defined response workflows
Operational Response
- incident response playbooks exist and are documented
- compromised endpoints can be isolated quickly
- backups allow fast system restoration
Managed infrastructure providers frequently implement these layered security controls across client environments. Firms such as Carefree Computing often focus on operationalizing privilege control, isolation, and monitoring so organizations maintain strong defenses even when individual protections are bypassed.
Practical takeaway:
Resilient security assumes failure and designs systems that limit damage when defenses are bypassed.
Frequently Asked Questions
Why is traditional antivirus no longer enough?
Traditional antivirus relies on detecting known malware signatures. Modern attacks frequently use polymorphic malware, legitimate administrative tools, or AI-generated variants that avoid known signatures. Because of this, organizations increasingly rely on behavioral detection, endpoint monitoring, and isolation techniques to detect suspicious activity.
What is an endpoint security strategy?
An endpoint security strategy is a comprehensive approach to protecting devices such as laptops, servers, and workstations. It typically includes behavioral monitoring, privilege management, isolation mechanisms, logging, and incident response procedures designed to detect and contain threats.
What does least privilege mean in cybersecurity?
Least privilege means granting users and applications only the permissions required to perform their tasks. By limiting administrative access, organizations reduce the damage attackers can cause if a device becomes compromised.
How does isolation improve endpoint security?
Isolation prevents compromised processes from affecting other systems. Technologies such as virtual machines, containers, and sandboxed environments allow risky workloads to run separately from critical systems, limiting the impact of malware or exploitation attempts.
What is endpoint detection and response?
Endpoint detection and response (EDR) platforms monitor system behavior to identify suspicious activity. Unlike traditional antivirus, EDR tools analyze system actions such as process execution, network connections, and privilege changes to detect potential attacks.
Conclusion
Security discussions often focus on blocking threats.
Experienced operators know that perfect prevention is unrealistic.
Attack techniques evolve faster than any single defensive tool.
That reality is why modern endpoint security strategies emphasize containment.
Behavior monitoring identifies suspicious activity. Isolation limits the spread of compromise. Least privilege ensures attackers cannot immediately control entire systems.
Together, these controls create an environment where breaches become manageable incidents rather than catastrophic failures.
Organizations that design their security architectures around this principle gain a powerful advantage.
Not because attacks disappear.
But because when they happen, the damage stays contained.
