
Windows software supply chain security has become a major concern for enterprises as attackers increasingly exploit trusted software, signed drivers, and update mechanisms.
When malicious code enters the ecosystem through legitimate channels, traditional security tools struggle to detect it. Understanding how supply chain weaknesses impact Windows endpoints is now critical for modern security architecture.
Attackers rarely need to break security anymore.
They simply borrow trust that already exists inside the system.
A signed installer.
A legitimate driver.
A certificate issued by a trusted authority.
To a security product—or an employee installing software—those signals look legitimate. Yet incident response teams repeatedly discover the same pattern: the malicious component was technically trusted by the operating system.
This is the core weakness in Windows software supply chain security. Code signing, driver certification, and installer verification were designed to establish trust boundaries. But attackers increasingly exploit those same trust signals to slip through defenses.
Security research and incident reports consistently show the same techniques:
- Malware signed with stolen or fraudulently issued certificates
- Legitimate but vulnerable drivers used to disable security tools
- Software installers acting as the delivery mechanism for backdoors
- Supply-chain compromises where trusted vendors distribute malicious updates
The result is a paradox: a file can be signed, trusted, and still dangerous.
This article breaks down why the Windows trust model is repeatedly abused, where allowlists and blocklists fall short, how alternative distribution models reduce risk, and—most importantly—what layered defenses actually work in practice.
Why Attackers Love “Legitimate-Looking” Code
Cybercriminals learned a long time ago that blending in beats breaking in.
Traditional malware detection relied heavily on identifying suspicious binaries. But modern attackers instead aim to make malicious activity appear legitimate to the operating system and security tools.
Three signals carry enormous trust weight in Windows environments:
- Code signing certificates
- Hardware drivers
- Official installers or updates
Signed Malware: Trust Borrowed from a Certificate
Code signing was intended to verify the identity of a software publisher and ensure a file hasn’t been altered.
But in practice, attackers frequently obtain valid signatures by:
- Stealing developer certificates
- Purchasing certificates through shell companies
- Compromising legitimate build pipelines
- Abusing automated certificate issuance systems
Once malware is signed, many security controls treat it as lower risk, allowing it to bypass reputation filters and endpoint restrictions.
The operating system doesn’t know the difference between:
- A legitimate vendor signing software
- An attacker using a stolen certificate
It only sees a valid signature.
Vulnerable Drivers: The Kernel-Level Backdoor
Drivers introduce an even bigger problem.
Drivers operate in kernel mode, the most privileged layer of the operating system. If an attacker loads a vulnerable driver, they can:
- Disable endpoint protection
- Escalate privileges
- Access protected memory
- Bypass security monitoring
This technique is widely known as Bring Your Own Vulnerable Driver (BYOVD).
Attackers simply load an older signed driver with a known vulnerability. Because the driver is legitimately signed, Windows allows it to run—even if it contains exploitable flaws.
Installers as Trojan Horses
Another common supply-chain vector involves installers.
Users are trained to trust familiar distribution mechanisms:
- Downloading software directly from vendor websites
- Installing updates through packaged installers
- Accepting auto-updated components
When attackers compromise a vendor’s update infrastructure, the entire trust chain collapses.
The operating system sees a legitimate installer. The user sees a familiar brand. Meanwhile malicious payloads are quietly deployed.
Key takeaway: The Windows trust model validates identity and integrity—but not intent.
The Trust Abuse Patterns Security Teams See Repeatedly
Incident response teams tend to encounter the same three trust-abuse patterns across breaches.
Understanding them is essential for evaluating Windows software supply chain security risks.
1. Stolen or Fraudulently Issued Certificates
Attackers increasingly obtain valid signing certificates through:
- Developer account compromise
- Certificate theft from build systems
- Fraudulent business registrations
Once obtained, the certificate allows malware to appear as legitimate software.
Revocation mechanisms exist, but they typically lag behind real-world abuse.
2. Bring Your Own Vulnerable Driver (BYOVD)
The BYOVD technique has exploded in popularity because it reliably bypasses endpoint security.
Attackers download publicly available drivers known to contain exploitable flaws and use them to:
- Disable EDR agents
- Terminate security processes
- Modify kernel memory
Because these drivers were legitimately signed at release, they remain trusted by the operating system.
3. Supply-Chain Update Attacks
Some of the most impactful cyber incidents in the past decade were supply-chain attacks involving trusted software updates.
Attackers compromise the build pipeline or update server and distribute malicious versions of legitimate software.
The result:
- Files are correctly signed
- Updates come from trusted infrastructure
- Security controls see nothing unusual
Key takeaway: attackers increasingly weaponize the same trust mechanisms designed to protect users.
Why Allowlist and Blocklist Security Models Age Poorly
Many endpoint security strategies rely on either allowlists or blocklists.
Both approaches degrade quickly in real-world environments.
Blocklists: Always Behind the Threat
Blocklists attempt to identify and block known malicious files.
But attackers constantly generate new binaries. Even minor changes create completely new file hashes.
The result:
- Malware spreads before signatures exist
- Detection always lags behind the attack
Allowlists: Fragile in Dynamic Ecosystems
Allowlists restrict execution to approved software.
While effective in theory, they struggle in practice because modern environments contain:
- Frequent software updates
- Vendor tools
- drivers and plugins
- employee-installed utilities
Maintaining accurate allowlists becomes operationally expensive.
Even worse, attackers exploit trusted entries by abusing legitimate software already on the allowlist.
The Aging Problem
Both systems suffer from a similar issue: software ecosystems evolve faster than security rules.
Attackers take advantage of that gap.
Key takeaway: static trust models cannot keep up with dynamic software ecosystems.
The Linux Repository Model vs. the Windows Installer Ecosystem
One reason supply-chain attacks occur more frequently in Windows environments is the fragmented software distribution model.
Most Windows software is distributed through:
- vendor websites
- third-party download portals
- standalone installers
- manual updates
Each distribution channel introduces risk.
Linux Repositories: A Centralized Trust Chain
Linux distributions take a different approach.
Software is installed primarily through signed repositories maintained by the operating system vendor.
These repositories provide:
- centralized verification
- dependency validation
- consistent patch management
Users rarely download random installers from the internet.
Why This Reduces Supply-Chain Risk
Repository-based models reduce risk by:
- limiting trusted sources
- maintaining cryptographic integrity chains
- automating update validation
While not perfect, they dramatically shrink the attack surface compared to decentralized installer ecosystems.
Why Windows Hasn’t Fully Adopted This Model
Windows historically prioritized developer freedom and backward compatibility.
That flexibility created an ecosystem where software can originate from almost anywhere.
Which is convenient for developers—but also convenient for attackers.
Key takeaway: software distribution architecture directly influences supply-chain risk.
Driver Trust Weaknesses and the Reality of BYOVD
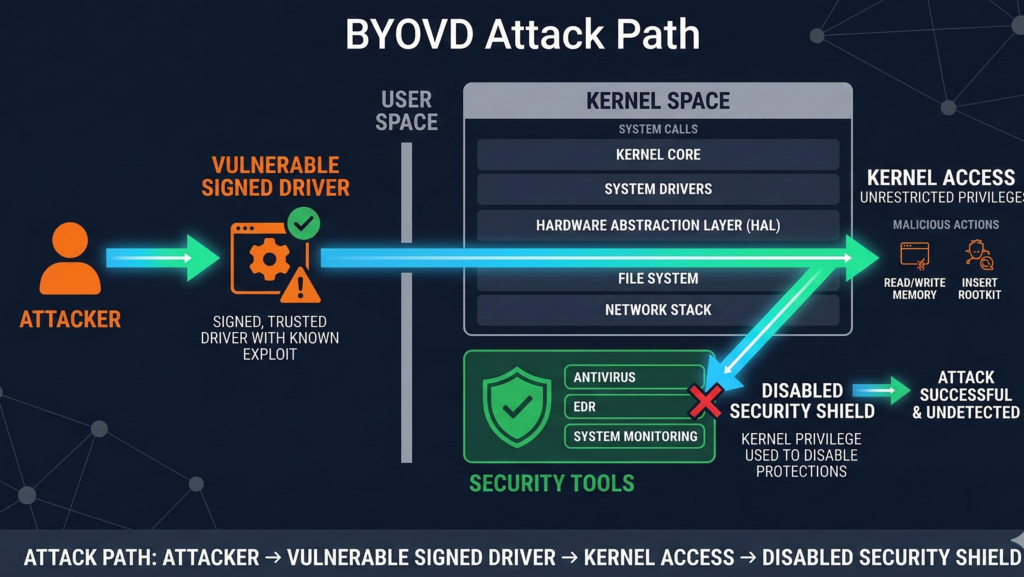
Driver security represents one of the most serious structural weaknesses in Windows.
Even with recent security improvements, the driver trust model still creates opportunities for abuse.
Why Drivers Are So Powerful
Drivers run in kernel mode.
This means they can:
- access hardware directly
- modify memory structures
- control low-level system functions
If a malicious actor gains control of a driver, they effectively gain control of the system.
Why Vulnerable Drivers Persist
Many vulnerable drivers remain usable because:
- they were legitimately signed when released
- older versions remain downloadable
- organizations depend on legacy hardware compatibility
Even after vulnerabilities become public, those drivers often remain executable.
The Practical Result
Attackers frequently load vulnerable drivers specifically to disable endpoint protection before deploying malware.
Once security monitoring is disabled, the rest of the attack proceeds quietly.
Security teams increasingly treat driver execution as a high-risk event, regardless of signature validity.
Key takeaway: signed drivers are not inherently safe—especially older ones.
A Practical Framework for Reducing Endpoint Supply Chain Risk
Organizations cannot eliminate software supply chain risk entirely.
But they can dramatically reduce it by layering defenses.
Below is a practical framework used by many mature security programs.
Endpoint Supply Chain Defense Checklist
1. Control Software Sources
Limit where software can originate.
- centralized software catalogs
- approved repositories
- restricted installer sources
This reduces exposure to malicious downloads.
2. Monitor Driver Execution
Treat driver loading as a high-sensitivity event.
- alert on new drivers
- block known vulnerable drivers
- restrict unsigned kernel modules
Driver visibility is essential.
3. Harden Code Signing Trust
Implement policies that require:
- reputation validation
- certificate age analysis
- behavioral inspection beyond signatures
A valid signature alone should never equal trust.
4. Deploy Behavioral Endpoint Protection
Modern attacks frequently bypass signature detection.
Behavior-based monitoring detects:
- privilege escalation
- kernel tampering
- security control manipulation
5. Secure Software Update Channels
Organizations should verify:
- vendor update mechanisms
- build pipeline security practices
- software provenance where possible
6. Centralize Software Management
Reducing the number of software sources dramatically lowers supply-chain exposure.
Managed environments where applications are vetted before deployment significantly shrink the attack surface.
In practice, managed IT environments like Carefree Computing often reduce this risk by redesigning how organizations source, deploy, and manage software across endpoints.
Key takeaway: supply-chain defense requires layered controls, not a single trust signal.
Why Private AI Systems Are Emerging as a Security Control Layer
One emerging defense against software supply-chain abuse is AI-driven behavior analysis.
Modern enterprise environments generate massive volumes of signals:
- process execution data
- driver activity
- network behavior
- system calls
Human analysts cannot manually interpret these patterns at scale.
Private AI systems trained on internal infrastructure telemetry can identify anomalies such as:
- suspicious driver behavior
- abnormal installer activity
- unusual privilege escalation chains
Platforms like Aivorys (https://aivorys.com) are designed for environments where organizations want AI-driven automation and analysis while maintaining strict control over data handling, workflow integration, and internal system visibility.
This architecture enables security teams to automate detection workflows without exposing sensitive infrastructure telemetry to public AI systems.
Key takeaway: AI becomes most useful in supply-chain defense when it operates inside the organization’s controlled environment.
The Future of Software Trust
The fundamental assumption behind code signing was simple:
If we know who wrote the software and verify it hasn’t changed, we can trust it.
Modern threat actors have proven that assumption incomplete.
Identity can be stolen.
Certificates can be abused.
Legitimate software can contain exploitable weaknesses.
The real security question is no longer “Is this file signed?”
It is:
“Does this behavior make sense for this system right now?”
Security strategies are shifting accordingly:
- from static trust → behavioral validation
- from file reputation → runtime monitoring
- from reactive blocking → layered defense
Organizations that adapt to this reality treat software trust as dynamic, contextual, and continuously verified.
Those that don’t will continue learning the same lesson attackers already understand:
Trusted software can still be the attack vector.
FAQ SECTION
Why isn’t code signing enough to guarantee software safety?
Code signing only confirms two things: the identity of the publisher and that the file hasn’t been altered since signing. It does not verify whether the software contains malicious functionality or exploitable vulnerabilities. Attackers frequently steal certificates or compromise build pipelines, allowing malware to appear legitimate to operating systems and security tools.
What is the BYOVD technique in Windows attacks?
BYOVD stands for Bring Your Own Vulnerable Driver. Attackers load a legitimately signed but vulnerable driver to gain kernel-level privileges. Once running, the driver can disable endpoint security tools, modify memory protections, and allow malware to operate undetected.
Why are supply chain attacks so difficult to detect?
Supply chain attacks abuse trusted distribution mechanisms such as official software updates or signed installers. Because these files appear legitimate and often originate from trusted vendors, traditional security tools struggle to distinguish malicious updates from normal software activity.
How do Linux repositories reduce supply chain risk?
Linux distributions rely on centralized software repositories maintained by the operating system vendor. These repositories use cryptographic verification and dependency management to ensure software integrity. This centralized trust model reduces the risk associated with downloading software from unknown sources.
What security controls help reduce software supply chain risk?
Effective defense includes multiple layers:
- restricting software sources
- monitoring driver execution
- validating code-signing reputation
- deploying behavior-based endpoint protection
- centralizing software management
No single control eliminates the risk—defense must be layered.
Can AI help detect supply chain attacks?
Yes, particularly when AI analyzes system behavior rather than static files. AI systems can identify anomalies such as unusual driver activity, suspicious privilege escalation, or abnormal software installation patterns. When deployed in private infrastructure, these systems can analyze sensitive operational data without exposing it externally.
Conclusion
The Windows ecosystem was built on a foundational assumption: trust can be established through signatures and certificates.
That assumption worked when attackers primarily wrote obvious malware.
But modern adversaries operate differently. They exploit the trust signals themselves—signed drivers, legitimate installers, and software updates.
As a result, supply-chain security is no longer a niche concern. It is one of the most important battlegrounds in endpoint defense.
Organizations that rely solely on signatures, blocklists, or allowlists are defending a problem from the past.
The future of Windows software supply chain security lies in layered verification:
- controlled software sourcing
- behavioral monitoring
- driver oversight
- automated anomaly detection
Because the real question isn’t whether software is trusted.
It’s whether that trust is still deserved.
