Trending Posts
Other Posts
Latest Posts
Don’t miss our hot and upcoming stories
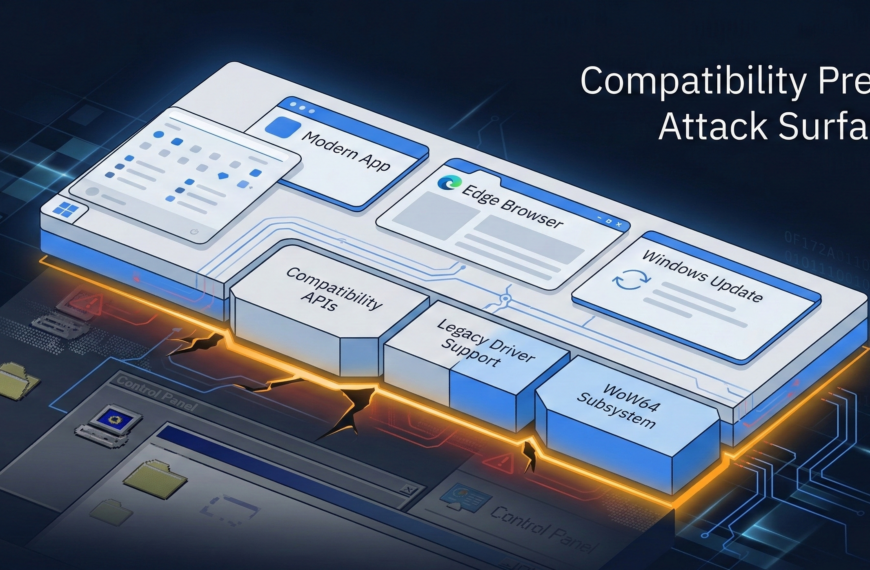
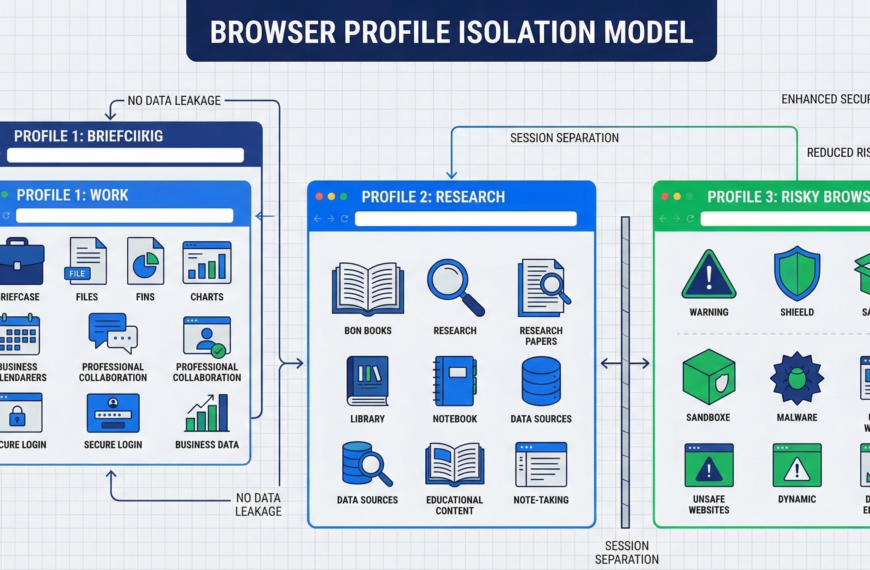
Secure Browsing on Linux: How to Reduce Phishing and Drive-By Risk Without “Security Theater”
Most organizations still treat the operating system as the center of security. That assumption is…
Linux for Compliance: Open Standards Reduce Audit Risk
Audits punish opacity. When auditors evaluate infrastructure, they rarely focus on the technology brand itself.…
Backup Strategy for Migrations: Prevent Data Loss & Ransomware
Most people discover they don’t have real backups after they need them. A migration fails.…
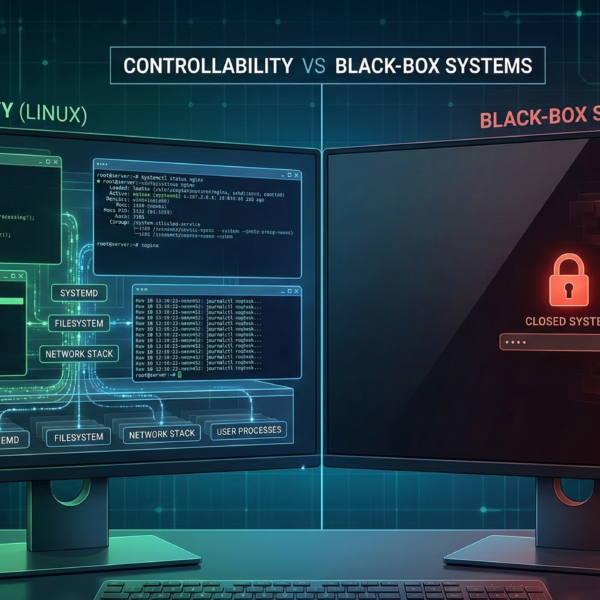
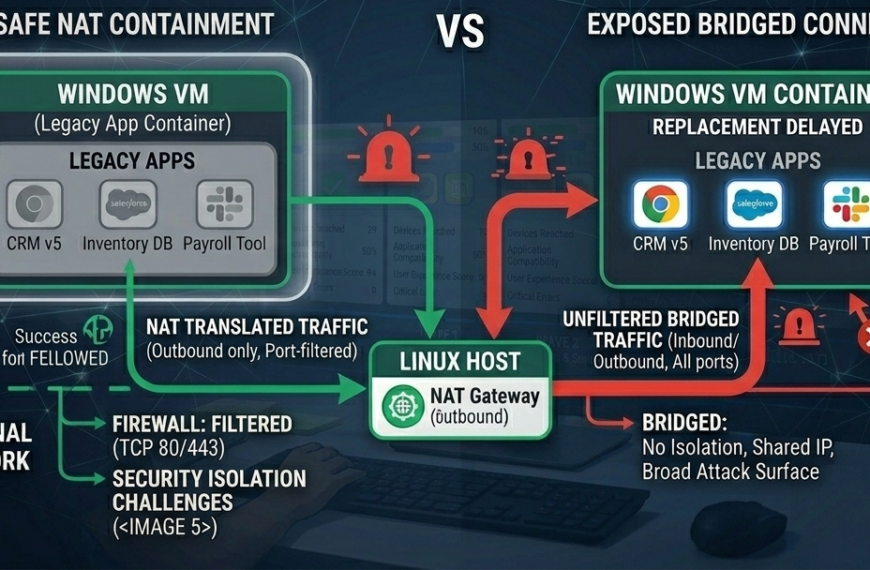
Virtualization Security Done Right: How to Prevent Your Windows VM From Reinfecting Your Linux Host
Many IT teams assume that running Windows inside a virtual machine automatically improves security. The…
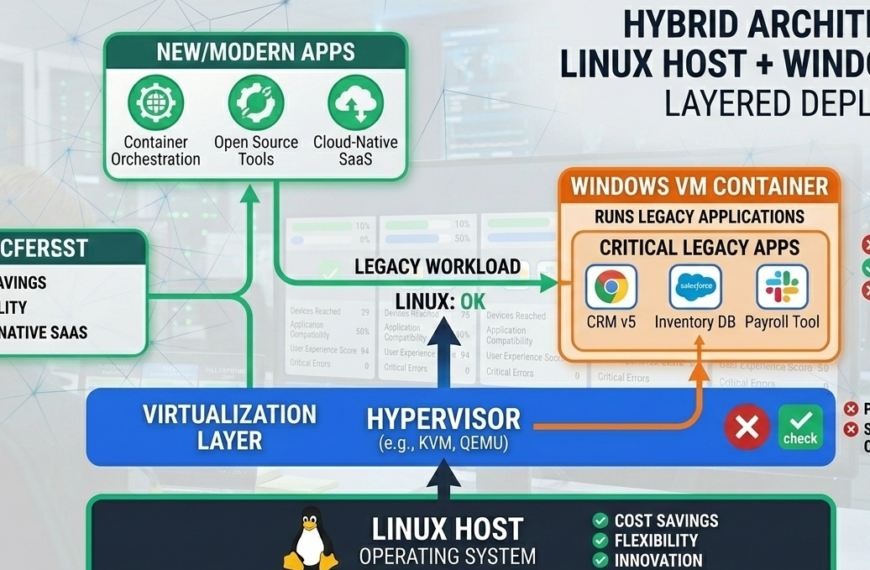
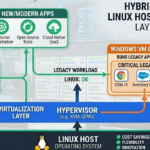
Hybrid Linux + Windows VM: Secure Path From Windows
The biggest obstacle to switching from Windows to Linux rarely has anything to do with…
Stop Replacing Laptops That Still Work
Your laptop still works. It runs your applications, handles your files, and supports your daily…